[安洵杯 2019]crackMe
32位无壳
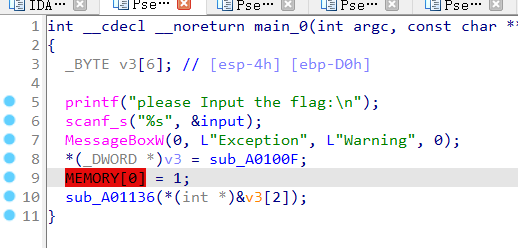
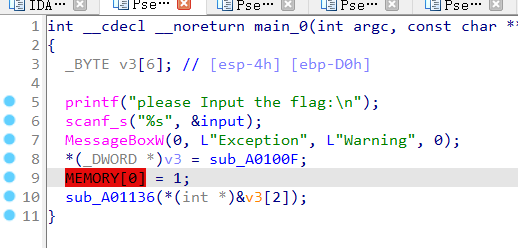
触发了异常处理——(向量化异常处理)VEH hook
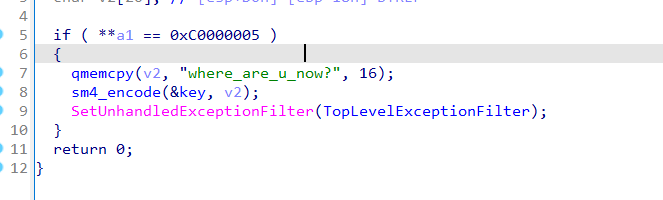
关键在于找到他的异常处理函数TopLevelExceptionFilter
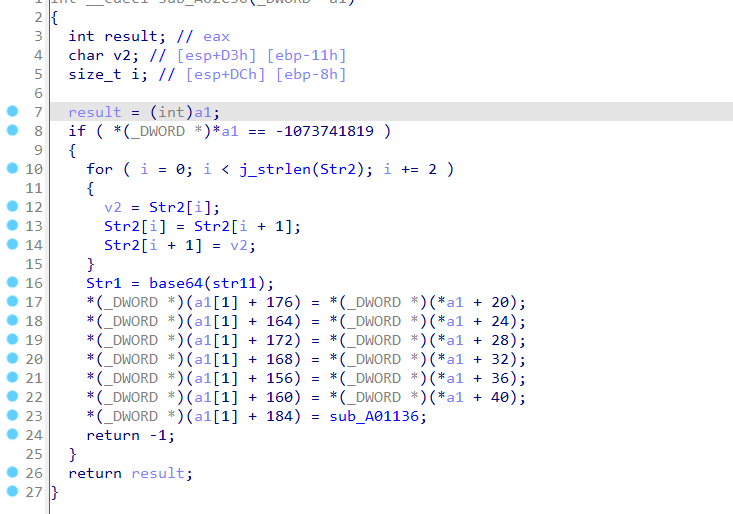
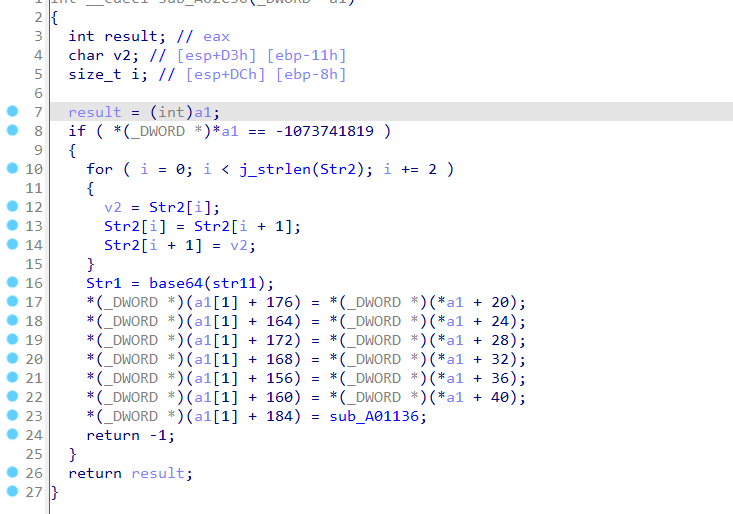
将str1base64加密后再与换位后的str2比较
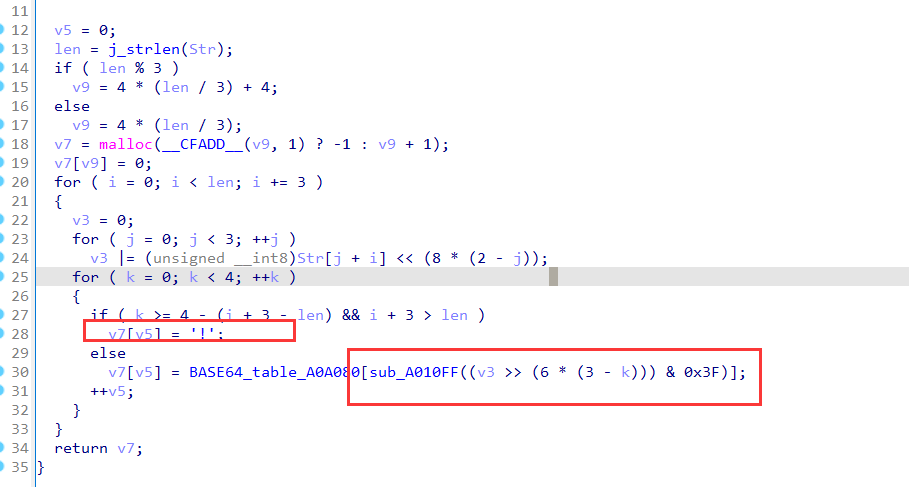
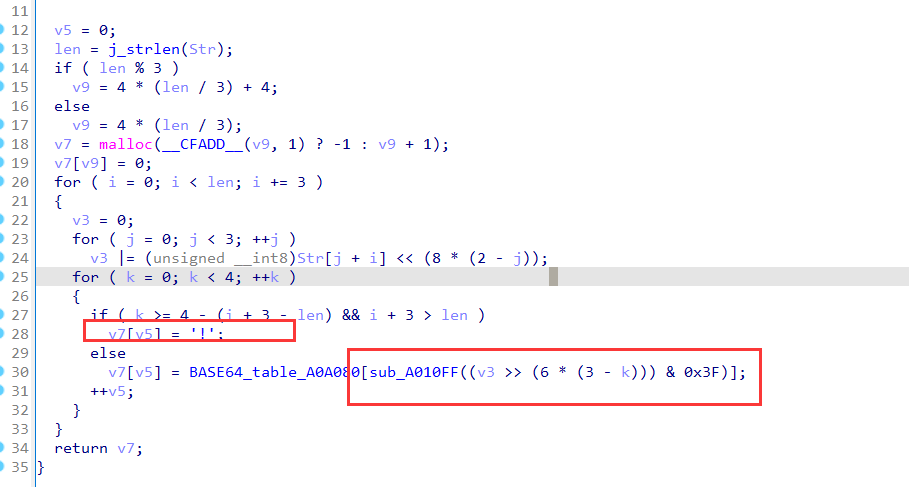
查看base64
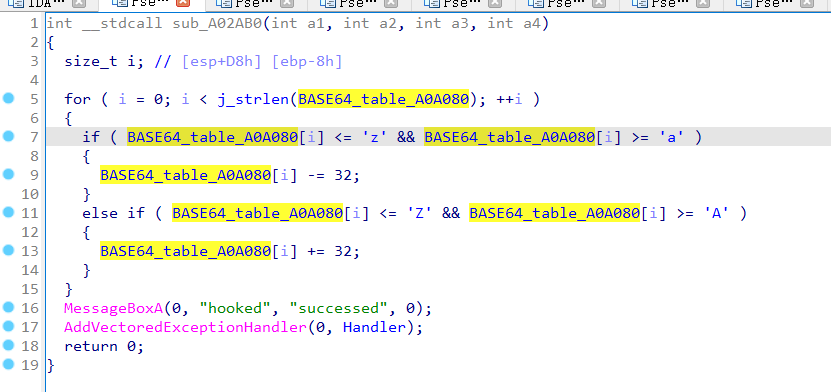
查看base64_table的交叉引用发现码表本身也被改动了
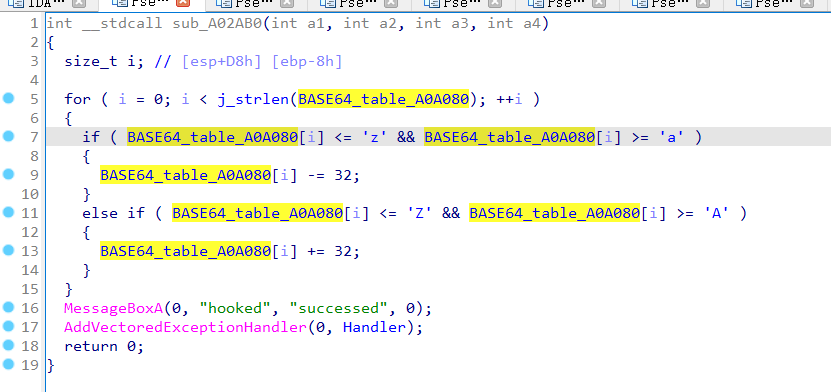
最后的结果就是将标准码表大小写转换后在循环向后位移24个字符
然后再去找输入
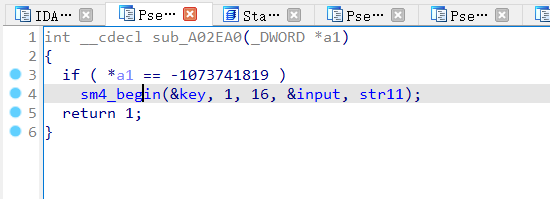
发现输入经过了一个sm4加密后被传到str11里面的
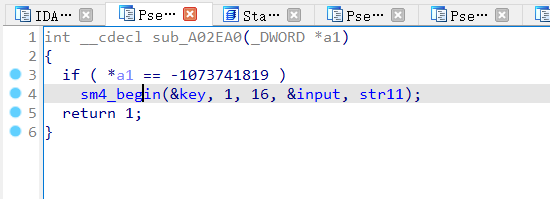
对这个key交叉引用
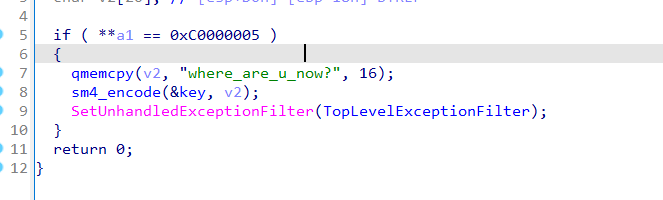
找到密钥
写脚本
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
| import base64
import pysm4
flag = "1UTAOIkpyOSWGv/mOYFY4R"
flag = list(flag)
for i in range(0, len(flag), 2):
flag[i], flag[i+1] = flag[i+1], flag[i]
for i in flag:
print(i, end="")
keyboard = 'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/'
keynext = ""
for i in range(len(keyboard)):
if keyboard[i] >= 'A' and keyboard[i] <= 'Z':
keynext += chr(ord(keyboard[i]) + 32)
elif keyboard[i] >= 'a' and keyboard[i] <= 'z':
keynext += chr(ord(keyboard[i]) - 32)
else:
keynext += keyboard[i]
keynext = keynext[24:] + keynext[0:24]
print(keynext)
change = ''
for i in range(len(flag)):
x = keynext.find(flag[i])
change += keyboard[x]
change += "=="
print(change)
sm4key = "where_are_u_now?"
x = base64.b64decode(change)
x = list(x)
for i in x:
print(hex(i), end=", ")
print()
for i in range(len(sm4key)):
print(hex(ord(sm4key[i])), end=", ")
hexflag = 0x59d095290df2400614f48d276906874e
hexkey = 0x77686572655f6172655f755f6e6f773f
deflag = pysm4.decrypt(hexflag, hexkey)
print('flag{'+bytes.fromhex(hex(deflag)[2:]).decode()+'}')
|